
Today I’ve attended an online discussion hosted by the CS50 professors David Malan and Brian Yu on how to keep your laptop and phone secure. Believe it or not, in 2019, the most common password used to “protect” systems and devices was 123456. The second one: 123456789. The third one: qwerty (take a look at your keyboard). The fourth one…”password”. The eighth one (my favourite): “iloveyou” 🙂
I’ve noted down here the takeaways:
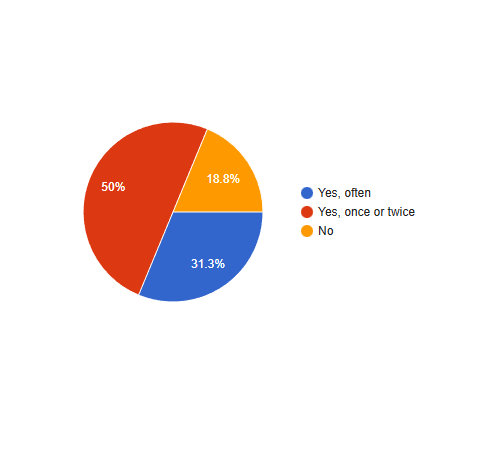
When is a device considered to be “secure”? We started by answering an online poll: Is your laptop/mobile secure? The majority was unsure (46%). That was also my response.
Do passwords keep your devices secure? It depends. Easy ones can be cracked by brute-force attacks. To carry out these attacks, hackers can program a script (e.g. in python) with an endless loop to, for example, try out all the possible combinations for 4-digit passwords (that is: 10x10x10x10 = 10000). One way to measure the security of a system is by counting the attempts somebody would need to crack the password.
An adversary would need a different amount of attempts to crack a password made of letters (English words). A standard English dictionary has about 140.000.
What if we change from 4-digit passcodes to 4-letter passcodes (letters of the alphabet)? The answer is 456,976 (26x26x26x26). That’s an improvement 🙂 But this is not secure enough.
Let’s try with alphanumeric characters (uppercase, lowercase, number, and characters) The results are much better: 14,776,336 (62x62x62x62). 62 results from 26 letters uppercase x 26 letters lowercase x 10 digits.
Tip: use uppercase, lowercase, digits, letters, and punctuation marks to configure your passwords. Why? 218,340,105,584,896 attempts might be required to brute-force it.
If it’s easy for a hacker to brute-force your device, what can be our defense against this kind of attack? You can use patterns, biometrics (face or digital recognition), disable the device after a certain number of guesses, etc…But to be honest, anything is too secure to prevent them from accessing your account 😦 However, a not so easy to hack password can act as a deterrent.
The downside of timeouts (“Too many attempts. Try again later”): you can lock yourself out of your phone and you might lose all your data if you don’t have a backup.
Another defense is the so-called two-factor authentication. How secure is this? It really narrows the scope of the threats because the hackers need physical proximity to your second device.
Do not use the same password on multiple websites or applications, it exposes you to more risks. If one website gets hacked and you are compromised, hackers do not even need to use brute-force, the just log in with the same password.
What about pass managers? Are they secure? Yes, because the information is encrypted. You only need to remember one master password (which must be really good. Otherwise, you are in trouble). You can also use random passwords created by your password manager. The tradeoff: the password manager might be also breached (if, for example, your master password is hacked or the software is buggy).
Where might encryption be compelling?
- End-to-end encryption (like WhatsApp -> Facebook cannot see my messages because they are encrypted)
- Https allows the servers to read the information you send and receive
The controversy around Zoom: they used https:// and not encryption at the beginning. To solve this, they acquired another company that implemented encryption. Zoom is still insecure (if you don’t add a password) because there is a pattern to generate the room links -> https://zoom.us/365273582. You might join a room randomly. However, on the other hand, this feature is user friendly because it is easier to enter ten digits instead of a much more complex alphanumeric sequence (balance between security vs user-friendliness). They don’t really deserve all the heat they took 😦
Allowing automate updates are also another way to secure your systems as well as full-disk encryption.
I’ve really enjoyed this session and, as always, learned a lot of new things 🙂




Leave a comment